Patch management is a strategic pillar of modern cybersecurity and operational resilience, shaping how organizations stay ahead of evolving threats in complex, multi-cloud environments and hybrid networks that blend on-premises infrastructure with remote endpoints. To stay ahead across data centers, cloud platforms, and distributed devices, teams implement patch management strategies and leverage robust patch management tools to orchestrate timely, validated updates, while maintaining visibility, rollback options, and compliance-ready reporting. From software patching to vulnerability remediation, these practices reduce exposure windows, preserve service continuity during patch cycles, and support auditable change control across diverse environments, supply chains, and evolving software ecosystems. In 2026, the emphasis is on automation, risk-based prioritization, scalable workflows, continuous monitoring, and governance-aligned processes that speed remediation without introducing new risk or regulatory friction for IT, security, and operations teams. This introductory guide highlights best practices for patch management and practical steps to accelerate safe remediation across Windows, Linux, macOS, and cloud workloads, while emphasizing measurable outcomes, repeatable processes, and traceable audit trails.
Viewed through an alternative lens, the topic translates to updates governance and security patching across devices, servers, and cloud services, emphasizing reliable delivery of security updates. LSI-friendly terms such as software updates, patching lifecycle, and vulnerability remediation capture the same discipline from different angles, enabling broader discoverability without changing the core objectives. Organizations can map these terms to concrete practices, including discovery, risk-based prioritization, automated deployment, and continuous verification. By aligning with IT operations and security teams, leaders can orchestrate seamless updates that close exposure gaps while preserving business continuity. In short, the mission remains the same: timely, trusted updates that protect assets, regulators, and customers.
1) Patch Management in 2026: Strategic Foundations for Modern IT Environments
In 2026, patch management is a strategic pillar that underpins cybersecurity resilience and operational reliability. Organizations must adopt robust patch management strategies that align with IT governance, risk management, and regulatory requirements to reduce exposure across hybrid environments. This approach emphasizes continuous discovery, risk-based prioritization, and rapid remediation to keep pace with evolving threats and complex software ecosystems.
Effective patch management requires a holistic view of assets, software versions, and dependencies, so patches reach the right targets without unintended disruption. By embedding vulnerability remediation into the core process, teams can shorten exposure windows and improve uptime. The goal is a repeatable, auditable workflow that scales across on-premises data centers, cloud platforms, and remote endpoints while meeting compliance mandates.
2) Choosing the Right Patch Management Tools for a Heterogeneous IT Landscape
Selecting the right patch management tools is essential when environments span Windows, macOS, Linux, containers, and cloud workloads. Patch management tools that provide cross-platform coverage, centralized reporting, and integrated vulnerability assessment help reduce tool sprawl and improve visibility. Native patching platforms (where available) should be complemented by cross-platform solutions to enable cohesive management across diverse ecosystems.
Evaluation should focus on automation capabilities, deployment orchestration, rollback support, and seamless integration with vulnerability management, change management, and CI/CD pipelines. A strong toolset enables phased rollouts, policy-driven enrollment, and auditable dashboards that demonstrate control effectiveness to regulators and stakeholders. Ensuring interoperability with existing security and IT operations tooling is critical to achieving efficient, scalable patching.
3) Best Practices for Patch Management: From Inventory to Automated Deployment
Best practices for patch management begin with normalization of asset data and comprehensive inventory. Accurate visibility is the foundation for targeting patches where they matter most and avoiding missed updates that create risk. Establishing a risk-based approach ensures that critical vulnerabilities receive prompt attention, even when patch cadence would traditionally slow response.
Automation plays a central role in scaling patching efforts, complemented by staged deployment and automated rollback. Implement standardized change control, maintain audit trails, and align patch processes with broader vulnerability management programs. Regular reviews of policies, thresholds, and KPIs help organizations continuously optimize coverage, success rates, and time-to-patch metrics.
4) Software Patching and Vulnerability Remediation in a Hybrid World
Software patching across diverse environments—on-prem, cloud, and containerized workloads—requires consistent processes that bridge multiple operating systems and deployment models. A unified patching strategy reduces fragmentation and ensures that critical updates reach every layer of the technology stack. Effective software patching helps close exposure gaps before adversaries can exploit them.
Vulnerability remediation should be integrated into the patching lifecycle, using risk scoring, CVSS guidance, and exploitability assessments to prioritize remediation. By coupling patch deployment with verification and attestations, teams can demonstrate compliance and strengthen security posture. Continuous monitoring and automated reporting keep stakeholders informed and support ongoing improvement.
5) Automating Patch Management with AI and Automation
Automation accelerates discovery, evaluation, deployment, and verification, reducing human error and freeing up teams to focus on higher-value security work. AI and machine learning can enhance patch management by predicting patch applicability, estimating risk, and optimizing deployment timing based on historical outcomes. This intelligent automation drives faster remediation while maintaining safety and governance.
Implementing AI-driven insights requires careful governance, human oversight, and clear policies for exceptions. Integrate automated workflows with change control processes and continuous vulnerability assessment to maintain trust and accountability. As systems scale, automation becomes essential to maintain speed, accuracy, and consistency across heterogeneous environments.
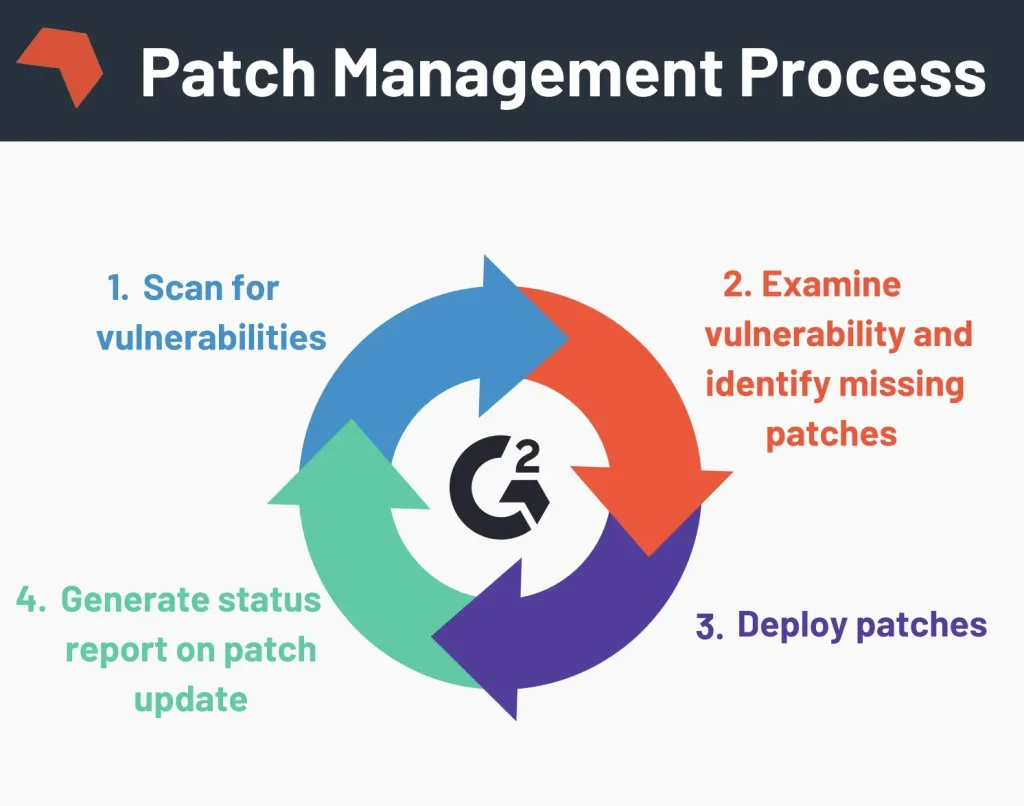
6) A Practical Patch Management Workflow: From Discovery to Verification
A practical workflow begins with automated discovery and inventory to identify missing patches, vulnerable software, and outdated configurations. Risk scoring helps prioritize which updates require immediate action, while testing in sandbox environments verifies compatibility with critical applications before broader deployment. This phased approach minimizes disruption while accelerating remediation.
Deploy patches in controlled waves, monitor deployment status in real time, and verify success with checksums, agent reports, or verification suites. Maintain audit-ready records and asset updates to support regulatory reporting and internal governance. Regularly review outcomes, refine thresholds, and iterate to close gaps in coverage, speed, and effectiveness.
Frequently Asked Questions
What is patch management and why is it essential in 2026?
Patch management is the continuous process of discovering software assets, prioritizing patches by risk, testing for compatibility, and deploying updates to fix vulnerabilities and improve system reliability. In 2026, patch management is a strategic pillar of cybersecurity and operational resilience due to hybrid environments, evolving threats, and expanding software ecosystems. Effective patch management relies on clear patch management strategies that balance risk, business impact, and deployment speed to minimize exposure.
How do patch management strategies reduce risk and downtime across hybrid environments?
Patch management strategies follow a risk-based, repeatable workflow: inventory and visibility, risk-based prioritization, testing and change control, deployment automation, verification and compliance, and continuous improvement. By prioritizing critical patches, testing in sandbox, and deploying in phased waves, organizations reduce downtime while lowering exposure to vulnerabilities.
What are patch management tools and how do they support cross-platform patching?
Patch management tools include native platforms (WSUS, Intune, Apple Software Update, and Linux package managers) and cross-platform solutions that patch Windows, macOS, Linux, and cloud workloads from a single console. They enable automated discovery, vulnerability prioritization, phased deployment with rollback, and centralized reporting—supporting software patching across diverse environments and vulnerability remediation.
What are the best practices for patch management in 2026?
Key best practices for patch management in 2026 include: normalizing asset data to build a reliable inventory; prioritizing patches by risk and business impact rather than cadence; automating patching where possible while preserving governance; using phased deployment with automated rollback; integrating patching with vulnerability management; preparing for zero-day and supply-chain threats; maintaining auditable records for compliance; and continuously measuring performance with KPIs to improve coverage and speed.
How does software patching relate to vulnerability remediation and compliance?
Software patching is the core mechanism for vulnerability remediation. A mature patching program verifies successful patch deployment, maintains audit trails, and demonstrates compliance with internal policies and external regulations through reports and dashboards. Aligning software patching with governance ensures timely remediation and regulatory readiness.
How can automation and AI improve patch management?
Automation accelerates discovery, assessment, deployment, and verification of patches, reducing manual effort and error. AI and machine learning can improve vulnerability scoring, predict patch applicability, and optimize deployment timing based on historical results. Implementing automation and AI within patch management tools supports faster vulnerability remediation and a stronger security posture.
| Key Point | Summary |
|---|---|
| Overview of Patch management in 2026 |
|
| Core components |
|
| Strategy |
|
| Tools & technologies |
|
| Best practices for 2026 |
|
| Challenges & how to overcome |
|
| Automation & AI in Patch management |
|
| Practical workflow example |
|
| Getting started |
|
Summary
Patch management in 2026 is a proactive, automated, and risk-aware discipline that strengthens cybersecurity resilience across hybrid IT landscapes. A mature Patch management program integrates people, processes, and technology to deliver timely remediation with minimal business disruption. By adopting robust strategies, leveraging the right tools, and following proven best practices, organizations can reduce exposure to threats, improve system reliability, and maintain operational continuity. As environments grow more complex and threat vectors expand, Patch management will be a defining factor in IT governance and business resilience.